위키 구독하기
Share wiki
Bookmark
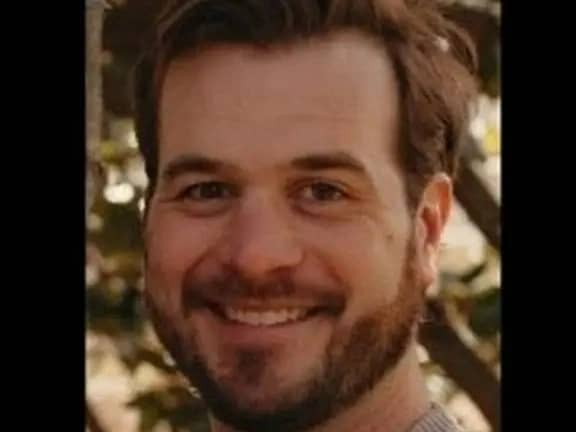
TJ Connolly
0%
TJ Connolly
T.J. Connolly는 Fireblocks의 수석 엔지니어이자 디지털 자산 인프라, 암호화폐 지갑 운영, 다자간 연산(MPC)을 전문으로 하는 사이버 보안 전문가입니다. 워싱턴 D.C.에 거주하며 애플리케이션 보안, 리버스 엔지니어링, 침투 테스트를 기반으로 경력을 쌓았습니다. [1]
학력
Connolly는 2011년 브라이언트 대학교에서 컴퓨터 과학 및 경영학 복수 전공으로 이학사 학위를 받았습니다. [2]
경력
Connolly는 2008년 브라이언트 대학교에서 파트타임 헬프 데스크 기술자로 경력을 시작하여 학업을 마치는 동안 학생들에게 기술 지원을 제공했습니다. 2010년에는 Fidelity Investments에 Unix 고가용성 엔지니어링 팀의 기술 인턴으로 합류하여 Red Hat Linux, Solaris 및 AIX 시스템에서 클러스터링 소프트웨어를 설치, 구성 및 테스트했습니다.
2011년 Connolly는 Booz Allen Hamilton에 수석 컨설턴트로 합류하여 국방부 및 상업 고객을 지원했습니다. 그의 책임에는 애플리케이션 및 네트워크 인프라 침투 테스트, 보안 코드 검토 수행, 시스템 강화 자동화 스크립트 개발, 침입 분석 및 네트워크 포렌식 수행이 포함되었습니다. 그는 2012년 Veracode로 옮겨 수석 애플리케이션 보안 컨설턴트가 되어 다양한 소프트웨어 환경에서 블랙, 그레이, 화이트 박스 침투 테스트를 수행하고 회사의 침투 테스트 관행 개발에 기여했습니다.
2014년부터 2016년까지 Connolly는 Independent Security Evaluators에서 수석 보안 컨설턴트로 근무했습니다. 이 역할에서 그는 엔터프라이즈 기술에 대한 보안 평가를 수행했으며, 리버스 엔지니어링, 디버깅, 개념 증명 익스플로잇 개발 및 코드 검토를 사용하여 디지털 권한 관리 시스템의 암호화 취약점에 중점을 두었습니다. 그런 다음 2016년 FireEye에 컨설팅 시스템 엔지니어로 합류하여 사이버 보안 이니셔티브를 지원하고 조직의 위협 탐지 및 사고 대응을 지원했습니다.
2020년 Connolly는 AffirmLogic의 영업 엔지니어링 이사가 되어 회사의 첫 번째 영업 엔지니어링 채용을 담당했습니다. 그는 자금 및 제품 문제로 인해 회사가 운영을 중단하기 전에 자동화된 리버스 엔지니어링 기술 상용화를 지원했습니다. 2021년에는 Contrast Security에 솔루션 아키텍트로 합류하여 애플리케이션 보호를 위한 보안 기술에 중점을 두었습니다. 2021년 12월부터 Connolly는 Fireblocks의 수석 엔지니어로 근무하며 디지털 자산 인프라 및 보안 분야에서 계속 일하고 있습니다. [5]
인터뷰
공격 벡터
2022년 8월 Connolly는 Mainnet 2022의 패널에 앞서 Messari의 Chase Devens와 다자간 연산(MPC)에 대해 이야기했습니다. Connolly는 사이버 보안, 애플리케이션 보안 및 침투 테스트 분야의 배경에 대해 논의하고 블록체인 및 탈중앙화 금융으로의 전환에 대해 설명하면서
잘못된 내용이 있나요?