Subscribe to wiki
Share wiki
Bookmark
CertiK
0%
CertiK
CertiK is a blockchain security company known for its expertise in smart contract audits and a comprehensive suite of security tools. Founded in 2018, CertiK focuses on increasing the safety and reliability of blockchain networks and smart contracts.
Overview
CertiK was founded in 2018 by professors of computer science from Yale University and Columbia University.[22] Co-founder Professor Ronghui Gu was awarded the VMware Systems Research Award in 2022[23] and is on the Monetary Authority of Singapore's International Technology Advisory Panel[24].
CertiK promotes a comprehensive approach to security, including smart contract audits, formal verification, penetration testing, and advanced security monitoring tools. The company is also actively involved in research and development, contributing to advancements in blockchain security for major companies including Apple[20], Samsung[21], and Sui[30].
CertiK has worked with over 4,000 enterprise clients, secured more than $360 billion worth of digital assets, and identified over 60,000 vulnerabilities in blockchain code. The company's clients include projects such as Aave[27], Polygon[26], BNB Chain[25], Aptos[28], and WEMIX[29].
CertiK makes all audit reports free and publicly available in an effort to raise the standard of security and transparency in Web3. Complete breakdowns of all vulnerabilities identified as well as whether they have been resolved can be found on a project's Skynet page.
CertiK's Security Suite
CertiK provides a number of other tools designed to help projects and investors take a well-informed and end-to-end approach to security and due diligence.
Skynet
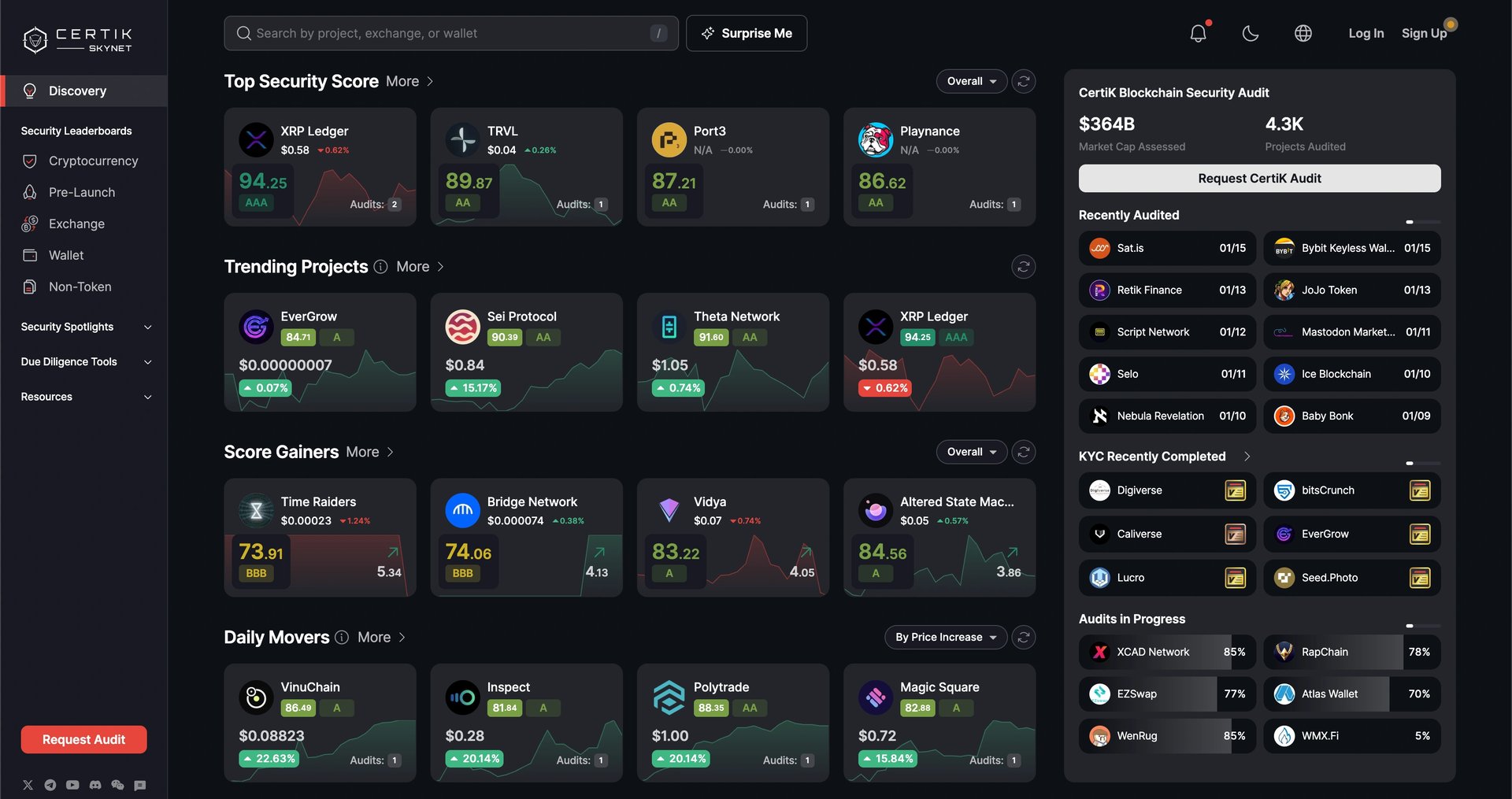
Security Score Leaderboard
CertiK’s Security Score Leaderboard lists and ranks projects according to their Security Score. The Security Score is generated using a proprietary algorithm that takes into account a project’s Code Security, Fundamental Health, Operational Resilience, Community Trust, Market Stability, and Governance Strength.
Verified Teams Leaderboard
The Verified Teams Leaderboard lists and ranks projects based on the status of their CertiK KYC Badge. Project teams that successfully undergo the background investigation are granted the CertiK KYC Badge, which comes in Gold, Silver, and Bronze.
Influencer Score Leaderboard
The Influencer Score Leaderboard lists and ranks Web3 influencers based on their influence score, which reflects the impact and reach of their content and online presence. This leaderboard is helpful for users who are interested in identifying influencers who are shaping the conversation in Web3.
Exchange Audit
Exchange Audit allows users to conduct due diligence on centralized exchanges (CEXs) by displaying the on-chain asset holdings in the wallet addresses controlled by the exchanges. This is an important first step for proof-of-reserve verification.
Skynet Alerts
Skynet Alerts is a system that provides timely notifications on exit scams and exploits in the cryptocurrency space. Skynet Alerts constantly monitors various sources of information to identify and report on potential rugpulls and exploits as they happen.
Smart Money Wizard
Smart Money Wizard is the access point for the Wallet Analyzer feature, and enables users to directly search for wallet addresses, view trending wallet searches, top smart money wallets, and top liquidity pairs. The Wallet Analyzer feature provides insights on wallet addresses and makes it easy to decipher on-chain transactions between wallets by displaying key wallet characteristics, visualizing wallet relationships and token trading activity.
SkyInsights
SkyInsights is a comprehensive crypto compliance and risk management platform. It offers wallet screening, real-time transaction monitoring, risk scores, and customizable alerts to help financial institutions, small-to-medium firms, and crypto-native platforms manage compliance complexities effectively. SkyInsights helps crypto-exposed organizations navigate regulatory landscapes efficiently while maintaining efficient processes and enhancing client trust.
KYC
CertiK KYC provides comprehensive and private identity verification for project teams. CertiK undertakes a live video call with each team member to verify their identity and other parameters as needed. As team anonymity increasingly enables high-risk behaviors, CertiK KYC helps to build accountability around projects to enable investors to move forward with confidence. Projects that earn a Bronze, Silver, or Gold KYC Badge demonstrate to their community that they are willing to stand publicly behind their project.
Penetration Testing
Penetration testing is the final component of a comprehensive approach to securing crypto applications in a runtime environment. CertiK's penetration testing services uncover vulnerabilities by leveraging proprietary tooling, powered by an experienced team of ethical hackers.
Bug Bounty
CertiK's Bug Bounty Program crowdsources intelligence from top ethical hackers to uncover vulnerabilities before malicious actors can exploit them. CertiK’s security engineers screen and qualify submissions and work with clients to implement the right fixes. The 0% fee model reduces the payout pressure for projects and allows white hat hackers to receive their full bounty.
SkyTrace
SkyTrace is a tracing tool to help analyze and visualize transaction data across Ethereum and BNB Chain wallets. This tool provides actionable insights into identifying and tracing suspicious flows to and from one’s own personal wallet or a project’s team wallet.
Advisory
CertiK Advisory offers a team of analysts who deliver technical evaluations, proprietary research, and strategy recommendations.
Supported Ecosystems
CertiK’s security services are available for all projects on all blockchains. A list of ecosystems the company has worked with includes:
- Algorand
- Aptos
- Arbitrum
- Avalanche
- BNB Chain
- Cardano
- Cosmos
- Cronos
- Ethereum
- Fantom
- Ferrum
- Harmony
- IoTeX
- Near
- OKTC
- Optimism
- Polkadot
- Polygon
- Solana
- Terra
- TON
- Tron
- WEMIX
- zkSync
CertiK Technology
Formal Verification
Formal verification involves the mathematical proof of a smart contract or blockchain protocol's functionality, ensuring it operates as intended without leaving any vulnerabilities undiscovered[31]. CertiK's approach to formal verification uncovers a broader range of vulnerabilities than what can be detected by human analysis alone.
The company's formal verification process prioritizes scalability, precision, and coverage. For popular smart contracts like ERC-20 and ERC-721, CertiK has automated the verification of common security properties, successfully applying this to hundreds of projects during their auditing phase. CertiK's formal verification enhances regular auditing by specifying and proving advanced custom security and correctness properties, such as the increase-K property of Automated Market Makers (AMMs), for complex smart contracts. Moreover, CertiK's formal verification extends to other blockchain building blocks including consensus protocols, and even basic systems infrastructure like the HyperEnclave TEE[32].
CertiK's approach to security auditing is defined by its use of manual code review, automatic verification, and custom formal verification. While manual code review and automatic verification are common in the industry, custom formal verification increases the effectiveness of auditing. In this process, security specialists create machine-readable specifications that are then mathematically verified by CertiK’s Custom Formal Verification system. This approach ensures a more effective security assessment, tailored to the unique features and languages of each project.
For blockchain protocols, CertiK provides customized solutions through formal verification of smart contracts and Decentralized Applications (dApps), aiming to foster a more functional and trustworthy blockchain ecosystem. The company's team of academics, researchers, and engineers develops highly customized solutions for each project, ensuring a thorough and effective auditing process.
DeepSEA
DeepSEA, developed by CertiK, is a formally verified compiler for smart contracts. It is as an advanced solution in the field of Web3 formal verification. It aims to address two critical issues: potential errors in the compiler, which could lead to security vulnerabilities in correctly written smart contracts, and inaccuracies in the verification toolchain, which might invalidate formal verification guarantees. The creation of DeepSEA is based on the recognition that as the verification gives more confidence in the logic of the program itself, it becomes increasingly important to ensure accuracy in the surrounding execution environment.
DeepSEA operates by taking contract source code written in high-level languages (like Solidity, Rust, Vyper, etc.) and translating it into executable bytecode for blockchain platforms (EVM, WebAssembly, etc.). The project stemmed from research on how to improve the execution environment, particularly focusing on the compiler aspect. DeepSEA is written in Coq's built-in programming language (Gallina) and is divided into multiple granular phases for enhanced verification efficiency.
DeepSEA supports two targets: EVM bytecode and Ethereum-flavored WebAssembly (eWASM). It is able to compile the DeepSEA surface language and serve as a backend for other smart contract programming languages. The verification of compiler correctness involves defining programming languages for input and output and their semantics, inventing and defining a 'match_states' relation between program states in the input and output languages, and proving that compiled program states align with the original program's states.
DeepSEA also integrates compilation and formal verification. This integration enables verifying programs at a high level while ensuring that the security properties verified are consistent with the compiled bytecode. As the technology progresses, CertiK's vision for DeepSEA is to have both compilers and verification tools operating on a unified core language with a formally verified compiler backend.
CertiK Partners and Collaborations
CertiK has established strategic partnerships with the leading digital asset exchanges, such as Binance[34], OKX[35], KuCoin[36], and Huobi[33].
In 2023, Sui awarded CertiK a five hundred thousand dollar bounty for identifying a critical vulnerability, nicknamed "HamsterWheel," which posed a risk to the entire blockchain.
CertiK verified The Open Network’s (TON) transaction per second record, demonstrating the chain's capacity for handling high-throughput blockchain projects[37].
The company successfully conducted formal verification of HyperEnclave, a project by Ant Group’s Trust Native Technology team, and audited XLS-30d[38], an Automated Market Maker (AMM) built on the XRP Ledger.
CertiK also formed a strategic partnership with Alibaba Cloud[39] aiming to bolster blockchain security in the realm of cloud computing. Additionally, the company joined forces with Finschia, serving as a governance member and node validator after conducting a thorough security review[40].
In humanitarian efforts, CertiK collaborated with Coala Pay to streamline funding, merging blockchain technology with social responsibility[41].
The firm extended its expertise to leading exchanges and wallet providers like OKX[43] and ZenGo[42], assisting them in resolving security vulnerabilities. The Skyfall team's mobile security research was acknowledged by Samsung, as evidenced by multiple CVEs, highlighting CertiK's influence in the broader cybersecurity landscape.
YZi Labs
On January 6, 2026, CertiK and YZi Labs partnered to established a $1M audit grant program for all participants in the EASY Residency incubation initiative.
This partnership supports the next generation of Web3, AI, and biotech startups by embedding security from day one. [44]
Education and Resources
CertiK also strives to provide both in-depth and accessible educational content in the field of Web3. Through its blog and various publications, CertiK aims to enlighten both industry experts and enthusiasts on the intricacies and evolving dynamics of blockchain technology and cybersecurity.
CertiK also publishes annual and quarterly Hack3d reports, which offer comprehensive statistics and detailed case studies. These reports are pivotal in understanding the current state of blockchain security, highlighting trends, vulnerabilities, and incidents within the blockchain space. CertiK's Hack3d reports serve as a crucial resource for developers, investors, and policy-makers, providing them with actionable intelligence and deeper insights into the challenges and opportunities in the realm of blockchain security.
See something wrong?
