0% read
Distributed Ledger Technology (DLT)
Distributed Ledger Technology (DLT)
**분산 원장 기술(DLT)**은 서로 다른 위치에 있는 컴퓨터가 네트워크를 통해 동기화된 방식으로 트랜잭션을 제안 및 검증하고 레코드를 업데이트할 수 있도록 하는 프로토콜 및 지원 인프라를 의미합니다.[2]
기술
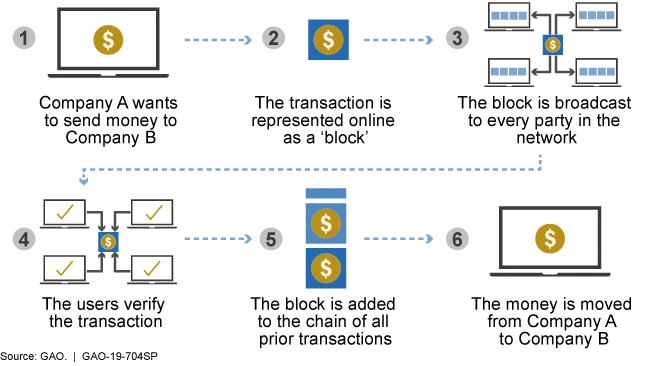
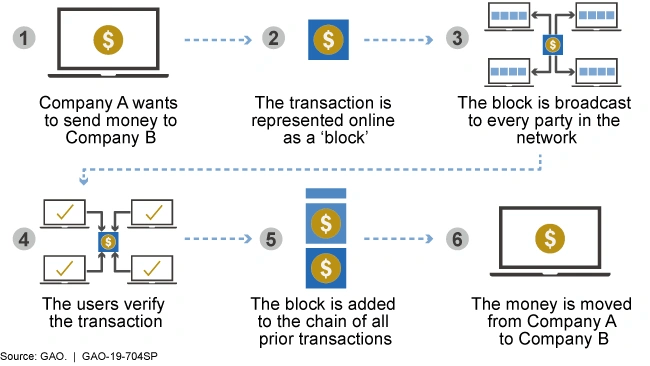
네트워크의 노드는 미리 정의된 규칙 및 프로토콜에 따라 트랜잭션의 유효성을 독립적으로 확인합니다. 일반적으로 확인에는 디지털 서명 확인, 발신자에게 필요한 권한이 있는지 확인, 트랜잭션이 네트워크 규칙을 준수하는지 확인이 포함됩니다.
확인된 트랜잭션을 원장에 추가하려면 네트워크가 합의에 도달해야 합니다. 다양한 DLT는 작업 증명(PoW), 지분 증명(PoS), BFT 등 다양한 합의 메커니즘을 사용합니다. 이러한 메커니즘은 원장에 추가되기 전에 대다수의 노드가 트랜잭션의 유효성에 동의하는지 확인합니다. 합의에 도달하면 확인된 트랜잭션이 블록에 추가됩니다. 이 블록에는 트랜잭션 그룹이 포함되어 있으며 연대순으로 이전 블록에 연결되어 블록체인이라고 하는 블록 체인을 형성합니다.
트랜잭션이 원장에 추가되면 변경 불가능하고 변조 방지 기능이 됩니다. 네트워크의 합의 없이는 정보를 변경하거나 삭제하는 것이 거의 불가능하므로 원장의 보안과 신뢰성이 매우 높습니다. 원장의 사본은 네트워크의 각 노드에 유지 관리됩니다. 이러한 중복성은 일부 노드가 오프라인 상태가 되거나 손상되더라도 원장의 무결성이 손상되지 않도록 보장합니다.
분산 원장은 계속 작동하여 지속적인 방식으로 새로운 트랜잭션 블록을 추가합니다. 이를 통해 원장 시작 이후의 모든 트랜잭션 또는 데이터 항목에 대한 완전하고 투명한 기록이 보장됩니다.[5]
DLT 유형
블록체인
이러한 유형의 DLT에서는 트랜잭션이 블록 체인 형태로 저장되고 각 블록은 유효한 트랜잭션의 증거로 사용할 수 있는 고유한 해시를 생성합니다. 각 노드에는 원장 사본이 있어 더욱 투명합니다.
허가형 DLT
노드는 네트워크에서 액세스하거나 변경하려면 중앙 기관으로부터 허가를 받아야 합니다. 대부분 이러한 유형의 권한에는 신원 확인이 포함됩니다.
Hyperledger Fabric은 개인 및 컨소시엄 블록체인을 위해 설계된 허가형 DLT로, 네트워크에 대한 액세스가 제어되고 신뢰할 수 있는 엔터티로 제한됩니다. 참가자는 네트워크에 가입하고 상호 작용할 수 있는 권한을 부여받아야 합니다.
무허가형 DLT
트랜잭션을 검증할 중앙 기관이 없으며 기존 노드가 트랜잭션 검증에 공동으로 책임을 집니다. 미리 정의된 알고리즘을 기반으로 트랜잭션을 검증하는 데 다양한 합의 메커니즘이 사용됩니다. 비트코인의 경우 작업 증명 합의 메커니즘이 사용됩니다.
비트코인은 공개 및 무허가형 블록체인에서 작동하므로 허가 없이 누구나 네트워크에 참여할 수 있습니다.
하이브리드 DLT
허가형 DLT와 무허가형 DLT가 결합되어 있으며 둘 다의 이점을 누릴 수 있습니다.
Corda Enterprise는 조직이 참가자를 알고 신뢰할 수 있는 개인 허가형 네트워크를 만들 수 있도록 하는 하이브리드 DLT 프로젝트입니다. 이는 금융 및 의료와 같이 엄격한 데이터 개인 정보 보호 및 규정 준수가 필수적인 산업에서 특히 유용합니다.
방향성 비순환 그래프(DAG)
DAG는 고유한 데이터 구조를 사용하여 데이터를 구성하므로 합의가 향상됩니다. 이러한 형태의 DLT에서 트랜잭션 유효성 검사는 네트워크의 대다수 노드의 지원에 크게 좌우됩니다. 모든 노드는 트랜잭션을 시작하기 전에 원장의 트랜잭션 증거를 제공해야 합니다. 이 시스템에서 노드는 자체 트랜잭션을 인증하기 위해 원장에서 최소 두 개의 이전 트랜잭션을 확인해야 합니다.
IOTA는 트랜잭션을 저장하기 위해 Tangle로 알려진 방향성 비순환 그래프(DAG) 구조를 사용하는 공개 분산 원장입니다.[1]
DLT 합의 메커니즘
작업 증명(PoW)
PoW에서 채굴자는 트랜잭션을 검증하고 새 블록을 생성하기 위해 복잡한 수학 문제를 해결하기 위해 경쟁합니다. PoW의 본질은 채굴자가 트랜잭션을 검증하기 위해 재정적 투자를 하고 리소스를 투입하여 인센티브를 제공해야 한다는 것입니다.[3]
PoW는 BTC 및 DOGE 암호화폐에 대해 비트코인 및 도지코인에서 사용됩니다.[7]
지분 증명(PoS)
PoS에서 검증자는 네트워크에서 지분을 보유하고 있으며 보유한 지분 금액에 따라 트랜잭션을 검증하도록 선택됩니다. 보다 환경 친화적인 옵션으로 간주되는 PoS는 51% 공격의 위험이 더 큽니다.[3]
PoS를 사용하는 프로젝트에는 이더리움 2.0, 카르다노, 테조스 및 폴카닷이 있습니다.
위임된 지분 증명(DPoS)
DPoS는 PoS의 변형으로, 네트워크에서 제한된 수의 검증자를 선택하여 트랜잭션을 검증합니다. 이 변형은 네트워크를 보호하는 데 필요한 계산 리소스를 줄입니다.[3]
DPoS를 사용하는 프로젝트에는 BitShares, TRON, Steem, Lisk, Ark 및 EOS가 있습니다.[6]
비잔틴 장애 허용(BFT)
BFT에서 검증자는 투표 시스템을 기반으로 합의 값에 동의합니다. 이 메커니즘은 분산된 당사자가 신뢰할 수 있는 중앙 당사자를 활용하여 합의에 도달해야 하는 게임 이론 문제를 설명하는 비잔틴 장군 문제를 피하기 위해 노력합니다.[3]
BFT를 사용하는 프로젝트에는 Hyperledger Fabric, Stellar, NEO 및 Ripple이 있습니다.
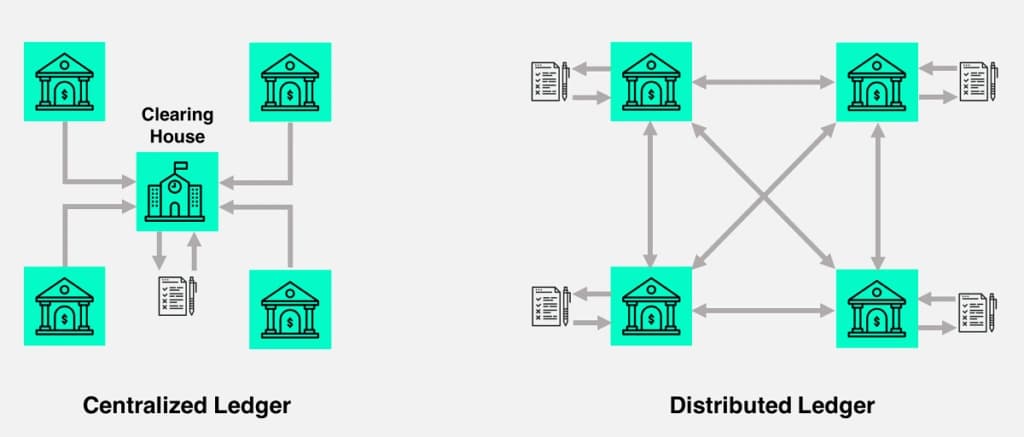
중앙 집중식 원장과 분산 원장 비교
| 원장/특성 | 중앙 집중식 원장 | 분산 원장 |
|---|---|---|
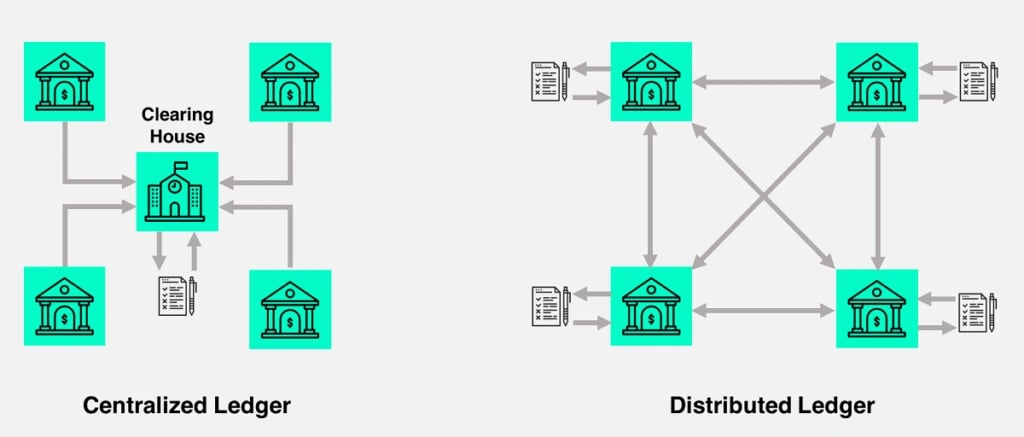
| 제어 | 단일 엔터티 또는 기관이 원장에 대한 완전한 제어 권한을 갖습니다. 이 엔터티는 원장을 유지 관리, 업데이트 및 관리할 책임이 있습니다. | 단일 중앙 기관이 없습니다. 데이터는 노드 네트워크에 분산되어 있으며 단일 엔터티가 원장에 대한 완전한 제어 권한을 갖지 않습니다. |
| 신뢰 | 신뢰는 중앙 엔터티의 명성과 무결성에 있습니다. | 신뢰는 계산, 암호화 및 네트워크 합의를 기반으로 시스템의 규칙 및 알고리즘에 있습니다. |
| 액세스 | 권한이 있는 개인 또는 엔터티만 원장을 보거나 수정할 수 있는 권한이 부여됩니다. | 누구나 네트워크에 참여하고, 원장을 보고, 트랜잭션을 검증할 수 있습니다. |
| 투명성 | 투명성이 떨어집니다. 데이터에 대한 액세스는 일반적으로 기관에서 필요하다고 판단하는 것으로 제한됩니다. | 투명성이 높습니다. 트랜잭션 데이터는 모든 참가자에게 표시되며 원장의 기록은 변경 불가능하고 변조 방지 기능이 있습니다. |
| 효율성 | 단일 제어 지점과 의사 결정이 있기 때문에 효율적이고 빠릅니다. 트랜잭션 및 데이터 업데이트를 신속하게 처리할 수 있습니다. | 효율성은 다양할 수 있습니다. 일부 원장은 속도보다 보안 및 분산화를 우선시하여 트랜잭션 처리 속도가 느려집니다. 다른 원장은 확장성 및 트랜잭션 속도 향상을 목표로 합니다. |
| 복원력 | 단일 실패 지점에 취약합니다. 중앙 기관에 문제가 발생하거나 손상되면 전체 원장의 무결성이 위험에 처합니다. | 실패 및 공격에 탄력적입니다. 단일 실패 지점이 없으므로 원장이 더욱 강력하고 안전합니다. |
| 예 | 기존 은행 시스템, 정부 기록 및 기업 데이터베이스 | 비트코인, 이더리움, Hyperledger Fabric 등 |
DLT의 응용 분야
DLT는 다양한 분야에서 응용 분야를 발견하여 산업과 프로세스를 변화시키고 있습니다.
금융
비트코인 및 이더리움과 같은 암호화폐는 DLT 유형인 블록체인을 활용하여 기존 금융 중개자를 우회하여 분산된 디지털 통화 트랜잭션을 가능하게 합니다.
공급망 관리
DLT는 제품 여정의 각 단계를 기록하여 공급망의 투명성과 추적성을 향상시킵니다. 이는 상품의 진위 여부를 확인하고 사기를 줄이는 데 특히 유용합니다.
의료
환자 기록, 제약 공급망 및 임상 시험은 DLT의 안전하고 변경 불가능한 데이터 스토리지의 이점을 누려 개인 정보 보호 및 데이터 무결성을 보장합니다.
투표 시스템
DLT를 사용하여 안전하고 투명한 투표 시스템을 만들어 선거 사기의 위험을 줄이고 민주적 프로세스의 무결성을 보장할 수 있습니다.
부동산
부동산 거래에는 종종 복잡한 서류 작업과 중개자가 필요합니다. DLT는 부동산 소유권을 안전하게 기록하고 이전하여 이 프로세스를 간소화할 수 있습니다.
국경 간 결제
DLT는 중개자를 제거하고 거래 수수료를 줄여 더 빠르고 비용 효율적인 국경 간 결제를 용이하게 할 수 있습니다.[4]
법률에 따른 DLT
DLT는 일반적으로 엔터티가 분쟁 해결을 위한 외부 메커니즘 없이도 거래할 수 있도록 합니다. 그러나 DLT 기반 서비스는 항상 관련 관할 구역의 법적 및 규제 프레임워크의 적용을 받습니다. 많은 관할 구역과 마찬가지로 호주에서는 법률 시스템이 계약 조건만으로 계약 집행을 허용하지 않는 시나리오가 있습니다.
예를 들어, 파산법은 해당 계약에서 해당 거래 발생을 고려했을 수 있는 경우에도 특정 상황에서 거래를 회수할 수 있도록 규정합니다. DLT 기반 서비스가 법률 내에서 작동할 수 있는지 확인하는 것이 중요합니다.[8]
잘못된 내용이 있나요?
평균 평점
2개의 평가를 기반으로
경험은 어땠나요?
빠른 평가를 해서 우리에게 알려주세요!
편집자
October 7, 2023. 12:12 UTC