위키 구독하기
Share wiki
Bookmark
Double Spending Problem
0%
Double Spending Problem
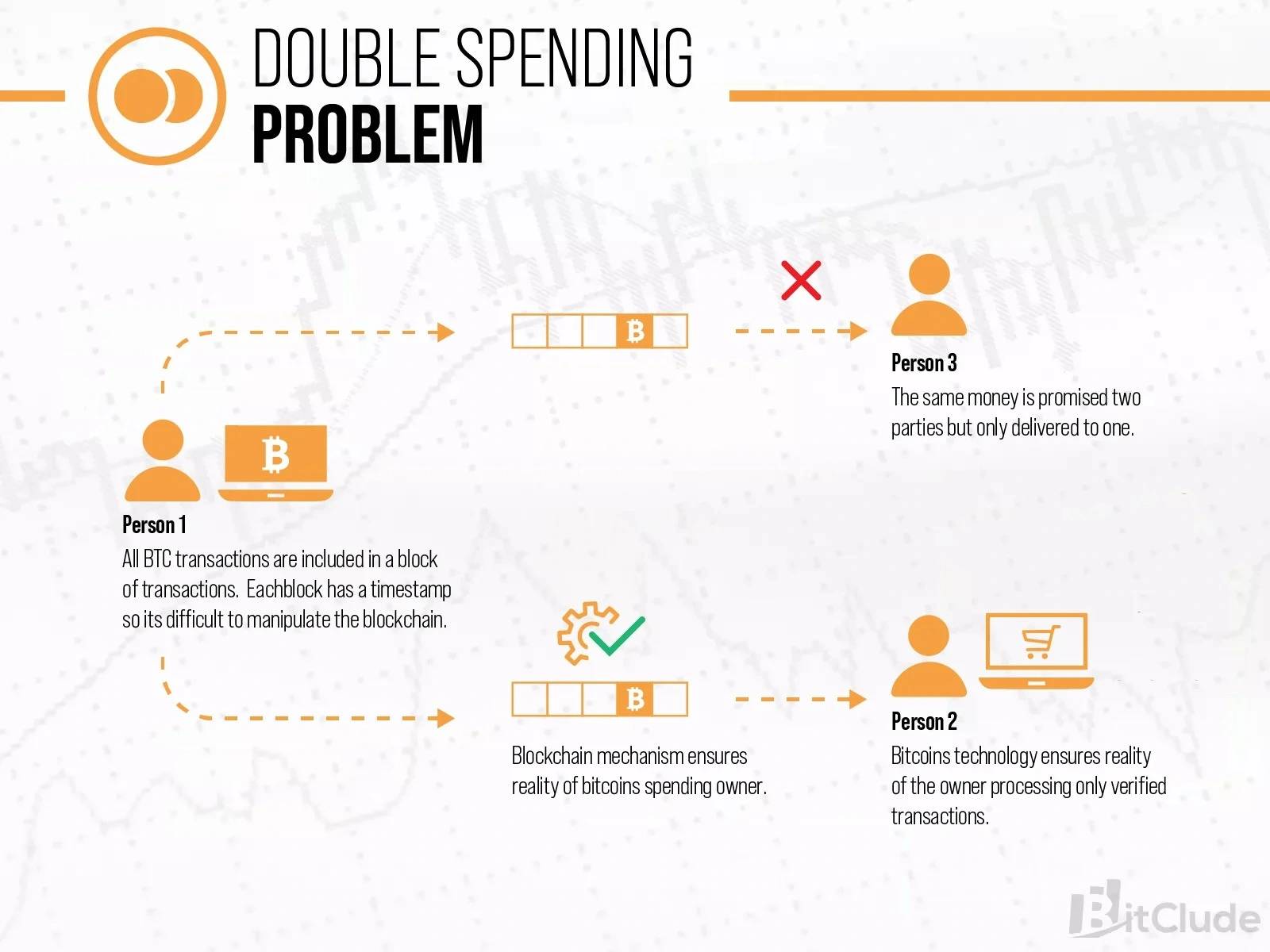
이중 지불 문제는 단일 통화 단위가 동시에 두 번 이상 사용되는 현상입니다. 이는 지출 기록과 사용 가능한 통화량 간의 불일치를 초래합니다. 이중 지불은 디지털 정보가 블록체인 프로토콜 작동 방식에 익숙한 숙련된 프로그래머에 의해 더 쉽게 조작되거나 복제될 수 있기 때문에 비트코인과 가장 일반적으로 관련됩니다. 비트코인은 또한 중개인이나 기관을 거치지 않는 P2P 교환 매체이기 때문에 도둑들이 이중 지불을 노리는 대상이기도 합니다.[1]
개요
예를 들어, 어떤 사람이 10달러만 가지고 옷 가게에 들어가 10달러짜리 셔츠를 산 다음, 이미 계산대에 지불한 동일한 10달러로 다른 10달러짜리 셔츠를 사는 경우를 생각해 봅시다. 실제 돈으로는 최근 거래와 현재 소유자를 실시간으로 쉽게 확인할 수 있기 때문에 이렇게 하기가 어렵지만, 디지털 통화로는 그렇게 할 가능성이 더 큽니다. 비트코인의 완전한 디지털 통화 네트워크는 탈중앙화되어 있어 도둑과 해커를 감시할 중앙 기관, 규제 기관 또는 관리 기구가 없습니다. 전통적인 보안 기관이 비트코인 네트워크에서 이중 지출을 감시하지는 않지만, 네트워크의 합의 메커니즘과 거래 원장을 위협할 수 있는 공격에 대처하기 위해 다른 네트워크 방어 수단이 구현되어 있어 비트코인에 투자하는 사람들에게 확신을 줍니다.
비트코인 이중 지불은 어떻게 작동하나요?
기본적으로 이중 지불은 악의적인 사용자가 하나의 거래 복사본을 보내 원본을 유지하거나 첫 번째 거래를 완전히 삭제하면서 복사본을 합법적으로 보이게 하는 것으로 구성됩니다. 디지털 정보는 복제가 더 쉽기 때문에 비트코인 또는 모든 디지털 통화에 가능하고 위험합니다. 범죄자들이 비트코인을 이중 지불하려고 시도하는 몇 가지 다른 상황이 있습니다.
동일한 비트코인 금액을 두 번 이상 동시에 보내기
공격자는 동일한 비트코인을 두 개(또는 그 이상)의 다른 주소로 동시에 보냅니다. 이러한 유형의 공격은 비트코인 네트워크의 느린 10분 블록 시간을 악용하려고 시도합니다. 이 시간 동안 트랜잭션이 네트워크로 전송되고 채굴자가 확인 및 검증하여 블록체인에 추가되도록 대기합니다. 추가 트랜잭션을 블록체인에 몰래 추가함으로써 도둑은 원래 비트코인 금액이 이미 소비되지 않았다는 환상을 주거나 기존 블록체인을 조작하고 원하는 미래의 이중 지출을 지원하기 위해 가짜 트랜잭션 기록으로 블록을 힘들게 다시 채굴할 수 있습니다.
이미 보낸 거래 되돌리기
공격자는 이미 보낸 거래를 되돌리기 위해 네트워크에 여러 패킷(데이터 단위)을 보내 거래가 발생하지 않은 것처럼 보이게 합니다. 이러한 방식으로 공격자는 상대방의 자산이나 서비스를 받은 후 거래를 되돌려 비트코인 이중 지불을 시도하여 받은 상품과 보낸 비트코인을 모두 유지하려고 합니다.
51% 공격
채굴자 그룹이 네트워크 해시율의 50% 이상을 통제할 때 암호화폐 블록체인에 대해 51% 공격을 가합니다. 네트워크 노드의 51%를 통제하면 관리 당사자가 블록체인을 변경할 수 있는 능력이 생깁니다. 공격자가 새로운 거래가 확인을 받지 못하도록 막을 수 있다면 일부 또는 모든 사용자 간의 지불이 중단될 수 있습니다. 또한 공격 당시 내렸던 결정을 되돌릴 수 있는 능력도 갖게 됩니다. 작업 증명과 같은 합의 시스템이 피하도록 설계된 문제 중 하나는 거래를 되돌려 사용자가 코인을 이중 지출할 수 있다는 것입니다.
높은 참여율을 가진 코인에 대한 51% 공격은 매우 까다롭고 어려운 작업입니다. 대부분의 경우 공격자 그룹은 필요한 51%를 확보하고 기회가 왔을 때 주입할 준비가 된 백업 블록체인을 보유해야 합니다. 그런 다음 주 네트워크는 해시 능력을 능가해야 합니다. 51% 공격에 대한 가장 큰 장애물 중 하나는 공격을 수행하는 데 드는 비용입니다. 예를 들어, Bitmain S19 XP Hydro는 가장 정교한 주문형 집적 회로(ASIC) 채굴기입니다. 255 TH/s(초당 테라 해시)의 해시율을 자랑하며 19,800달러가 넘는 비용이 듭니다. FoundryUSA는 54.42 EH/s(초당 엑사 해시)로 전체 비트코인 네트워크 해시율의 23.75%를 차지하고, AntPool은 41.49 EH/s로 18.12%, Binance Pool은 34.48 EH/s로 15.06%를 차지합니다. [2]
Finney Attack
피니 공격은 Hal Finney의 이름을 따서 명명되었으며, 그는 Bitcoin 거래의 첫 번째 수신자이자 Bitcoin 소스 코드 릴리스에 대해 처음으로 언급한 사람이었습니다. 이는 다음과 같은 특징을 가진 이중 지불 공격입니다.
- 상인이 확인되지 않은 거래를 수락하는 경우에만 작동합니다.
- 상인이 네트워크의 모든 사람이 자신이 지불받았다는 데 동의하는지 확인하기 위해 몇 초 동안 기다려도 여전히 작동합니다.
- 공격자가 자신의 블록 내용을 채굴하고 제어해야 합니다. 그러나 이론적으로는 모든 해시율로, 특히 네트워크 해시율의 50%보다 훨씬 적은 해시율로 이를 수행할 수 있습니다.
다음과 같이 진행됩니다.
- 공격자는 정상적으로 블록을 채굴합니다. 찾으려는 블록에서 이 거래를 브로드캐스트하지 않고 자신의 코인 일부를 자신에게 다시 보내는 거래를 포함합니다.
- 블록을 찾으면 브로드캐스트하지 않고 동일한 코인을 상품이나 서비스에 대해 상인에게 보냅니다.
- 상인이 지불을 수락하고 서비스를 되돌릴 수 없이 제공한 후 공격자는 자신의 블록을 브로드캐스트합니다. 이 블록에 포함된 코인을 자신에게 보내는 거래는 상인에게 지불되지 않은 지불을 무효화합니다.
블록을 찾는 시간부터 공격자가 지불을 보내고 상인이 수락할 때까지의 시간이 't'이고 블록을 찾는 평균 시간이 'T'인 경우 이 시간 동안 네트워크에서 다른 블록이 발견될 확률은 t/T입니다. 이 경우 공격은 실패하고 공격자는 B의 블록 보상을 잃게 됩니다. 즉, 공격 시도의 평균 비용은 약 (t/T) * B입니다. 일반적으로 상인은 이 공격을 수행하는 것이 수익성이 없는지 확인하기 위해 최소 t=V*T/B(V는 거래 가치)를 기다려야 합니다. 그러나 민첩한 공격자는 동일한 블록을 여러 공격에 사용하여 잠재적으로 총 가치를 얻을 수 있으므로 충분하지 않을 수 있습니다. 공격자의 해시율이 낮을수록 공격을 수행할 기회가 줄어듭니다. 공격이 비유동적인 상품을 얻기 위한 것이라면 이 상품에 대한 필요성이 블록을 찾는 것과 일치하기 어렵습니다. 공격이 유동적인 것(예: 비트코인을 다른 돈으로 교환)을 얻기 위한 것이라면 기회는 항상 존재하지만 상인은 몇 번의 확인을 요구할 가능성이 높습니다. 따라서 실제로 사용하기 어렵습니다.[4]
레이스 공격
레이스 공격은 이중 지불 시도의 특정한 종류로, 동일한 자금을 사용하여 동시에 두 개의 트랜잭션을 생성하여 두 번 지출하는 악의적인 활동입니다. 이는 수신자가 확인되지 않은 트랜잭션에 대한 지불을 수락하도록 요구합니다. 공격자는 피해자에게 확인되지 않은 트랜잭션을 보냅니다. 한편, 그들은 네트워크에 상충되는 트랜잭션을 브로드캐스트합니다. 피해자는 자신의 트랜잭션을 먼저 관찰했기 때문에 지불받을 것이라고 믿습니다. 그러나 네트워크의 나머지 부분이 이중 지불을 먼저 보았기 때문에 피해자가 돈을 받지 못할 가능성이 높습니다. 이러한 공격은 공격자가 피해자의 노드에 직접 연결되어 있고 상충되는 트랜잭션을 채굴자에게 직접 예치할 때 수행하기가 훨씬 쉽습니다.[6]
이중 지불 문제 방지 방법
사토시 나카모토의 백서에서는 이중 지불 문제에 대한 해결책으로 타임스탬프 서버가 제시되었습니다. 이 서버는 트랜잭션 블록을 해싱한 다음, 해당 해시를 비트코인 네트워크의 모든 노드에 브로드캐스트합니다. 이 타임스탬프는 해시 내의 어떤 정보도 해시 발행 이후에 생성될 수 없었음을 증명합니다. 이는 각 타임스탬프가 해시에 이전 타임스탬프를 포함하기 때문에 트랜잭션이 발생한 순서대로 변경 불가능한 로그를 생성합니다. 각 타임스탬프는 이전 타임스탬프를 기반으로 구축됩니다. 결론적으로, 블록체인은 트랜잭션 그룹을 비트코인 네트워크의 모든 노드에 브로드캐스트하고 타임스탬프를 찍어 이중 지불을 방지합니다. 트랜잭션은 블록체인에 타임스탬프가 찍히고 이전 트랜잭션과 양적으로 연결되어 있기 때문에 되돌릴 수 없으며 위조하기 어렵습니다.[2]
비트코인
2009년에 첫 번째 비트코인 클라이언트가 출시된 이후, 비트코인의 블록체인은 이중 지출을 방지하는 방법을 제대로 이해하기 위해 지금까지 수행된 모든 거래의 완전한 기록을 보존해 왔습니다. 모든 거래가 이전 블록에 암호화 방식으로 해시되므로 누구도 기록을 변경할 수 없습니다. 이 데이터베이스는 블록체인이라고 불리는데, 새로운 거래 묶음인 블록이 10분마다 추가되기 때문입니다.
이더리움
이중 지출을 피한다는 것은 동일한 금액을 두 번 사용하는 것을 막는 것을 의미합니다. 논스(nonce)가 동일하게 설정되면 트랜잭션 중 하나만 채굴되며 대부분 가스 가격이 더 높은 트랜잭션이 채굴될 수 있지만, 어떤 경우든 결국에는 하나의 트랜잭션만 발생하므로 이중 지출은 발생하지 않습니다.[3] 이더리움에는 두 가지 유형의 논스가 사용됩니다.
- 계정 논스 단순히 계정의 트랜잭션 횟수입니다. 이는 예를 들어 A에서 B로 20개의 코인을 보내는 트랜잭션이 B에 의해 반복적으로 재생되어 A의 잔액을 계속 고갈시키는 리플레이 공격을 방지합니다.
- 작업 증명 논스 작업 증명이 충족되도록 하는 데 사용된 블록의 임의 값입니다(당시 난이도에 따라 다름). 작업 증명 논스는 작업 증명 조건을 충족하기 위해 조정할 수 있는 블록의 의미 없는 값입니다.
사례
2019년 12월, 비트코인을 허용하는 장소에서 비트코인이 이중 지출되는 것을 보여주는 바이럴 비디오가 공개되었습니다. 이러한 공격은 비트코인 프로토콜에 대한 다소 논란이 있는 업그레이드인 RBF(Replace-By-Fee)를 사용하여 가능했습니다. 첫 번째 거래는 판매자에게 보내졌고, 그 다음에는 더 높은 수수료가 첨부된 두 번째 거래가 이어졌습니다. 이 RBF 거래는 더 높은 수수료가 우선적으로 처리된다는 것을 의미했기 때문에 첫 번째 거래를 무시하여 이중 지출이 가능했습니다. 이러한 공격은 판매자가 확인되지 않은 거래를 수락했기 때문에 작동했습니다.
비슷한 사건으로, 같은 해 초에 일부 캐나다 비트코인 보유자들은 실제로 비트코인을 현금화하지 않고도 '현금화'할 수 있었습니다. 그들은 비트코인 ATM으로 비트코인을 보내 현금을 인출할 수 있었던 것으로 보입니다. 현금을 받은 후, 그들은 아직 '확인'되지 않았기 때문에 거래를 취소했습니다. [5]
잘못된 내용이 있나요?