Subscribe to wiki
Share wiki
Bookmark
Multi-signature Wallet (multisig)
0%
Multi-signature Wallet (multisig)
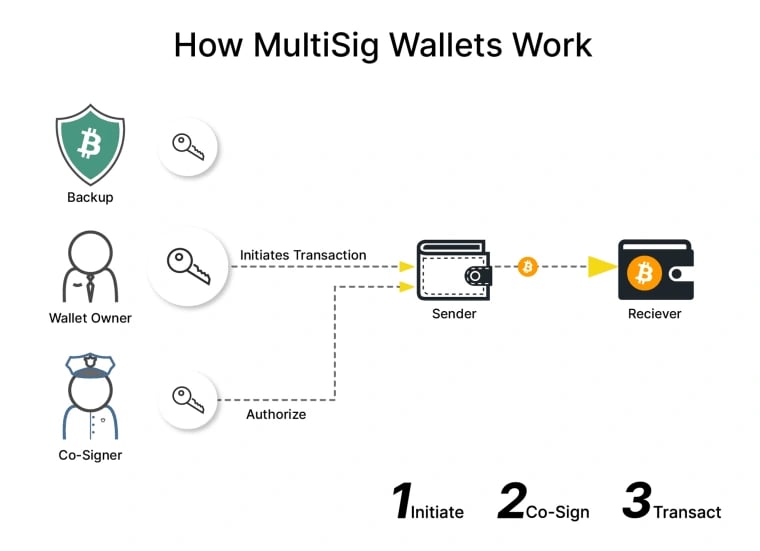
A Multi-signature Wallet or a multisig wallet is a cryptocurrency wallet that requires multiple signatures, instead of just one, to execute each transaction. Unlike traditional wallets, which rely on a single private key, multisig wallets demand multiple private keys for transaction authorization and completion.[1]
Types
Commonly used types of multisig wallets are:
n-of-n MultiSig Wallet
Transactions require more than one key for authorization. All keys must be used to create the signature. Examples include 2-of-2 multisig wallets, 3-of-3 multisig wallets, and so on. For example,
- 2-of-2 MultiSig wallet: this kind of wallet, fortified with two-factor authentication, employs the 2-of-2 multi-signature algorithm. It stores private keys on two distinct devices. For instance, one private key might be on a computer, while the other is on a mobile device. Transactions cannot proceed without signatures from both devices. While the 2-of-2 MultiSig wallet bolsters security, it poses a risk of losing access to the funds if one device becomes compromised.[1][2]
n-of-m MultiSig Wallet
Transactions demand some keys but not necessarily all for authorization. Examples include 1-of-2 multisig wallets, 3-of-5 multisig wallets, etc. For example,
- 3-of-5 MultiSig wallet: this MultiSig wallet variant necessitates 3 out of 5 available private keys to validate transactions. Exchanges often deploy them to augment the security of their hot wallets. An exchange endorsing 3-of-5 MultiSig addresses retains one private key online and reserves the second offline on a disconnected device. Meanwhile, a distinct security company holds the third key, a spouse or guardian may have the fourth, and another device might store the fifth. With three different entities governing the private keys, hacking one won't compromise the wallet. The offline backup further safeguards the hot wallet, especially if the security partner becomes defunct.[1][2]
Hardware MultiSig Wallets
Some hardware wallets, which are considered one of the most secure ways to store cryptocurrencies, offer multisig functionality. Hardware wallets are physical devices that store private keys offline, and when combined with multisig, provide an extra layer of security.
Software MultiSig Wallets
Many cryptocurrency wallets offer software-based multisig functionality, making them accessible to a broader audience. These wallets can be used on various devices, including desktop computers and mobile phones.
Custodial MultiSig Wallets
Some cryptocurrency exchanges and custodial services offer multisig wallets for added security. In this case, the exchange or service provider holds one of the private keys, while the user holds the others, ensuring that both parties must agree to transactions.
Smart Contract MultiSig Wallets
Some blockchain platforms, like Ethereum, allow users to create multisig wallets using smart contracts. These smart contracts can be programmed to enforce complex rules and conditions for transaction authorization.
Cold Storage MultiSig Wallets
Cold storage multisig wallets are typically created and stored in offline environments for maximum security. The private keys are generated and stored on devices that are not connected to the internet, making them highly resistant to hacking.
Cross-Currency MultiSig Wallets
Some multisig wallets support multiple cryptocurrencies, allowing users to manage different digital assets securely in a single wallet.[5]
Tech
A multisig wallet is established with a predetermined number of authorized signers, each with its own private key. When a transaction is initiated, it's broadcast to the blockchain network but remains unconfirmed until the necessary signatures are provided. This wallet enforces a signature requirement based on a predefined quorum.[1]
For example, in a 2-of-3 multisig wallet, two out of the three signers must provide their signatures. The authorized signers examine the transaction and affix their digital signatures using their private keys. Once the requisite number of signatures is secured, the transaction is confirmed, and the cryptocurrency gets transferred.[1][3]
Features
- All copayers can view the wallet's funds and transactions.
- Transactions from the wallet require signatures from one or more copayers, enhancing fund security.
- Each copayer is provided with a unique recovery phrase. However, if a recovery phrase for any copayer is lost, there may not be enough signatures to authorize transactions. Without sufficient copayers to sign, the wallet's funds become inaccessible.
- The wallet supports storing multiple cryptocurrencies under a single multisig key.[5]
Benefits
Enhanced Security
Multisig wallets provide superior security compared to single-signature wallets. Even if one private key is compromised, an attacker can't access the funds without the mandatory additional signatures.
Reduced Risk of Human Error
Requiring approvals from multiple individuals or entities, multisig wallets mitigate the risks of accidental losses or unauthorized transfers.
Protection Against Insider Threats
Within business or organizational contexts, multisig wallets defend against insider malicious actions, as it would necessitate collaboration among several insiders to jeopardize funds.
Two-factor Authentication (2FA)
Multisig wallets inherently act as a form of two-factor authentication (2FA). Designated signers must confirm any transaction-in-waiting. If a malicious actor gains unauthorized access to a key, users can promptly halt and revoke their reach. Amplifying this security measure, private keys are often stored across various locations or held by distinct individuals.
Escrow Services
Frequently, multisig wallets are utilized for escrow services. They retain funds until specific conditions are satisfied, presenting a transparent and fortified method for transactions.
Business Use Cases
In the corporate world, multisig wallets prove invaluable for treasury management. They enable a consortium of executives to monitor and endorse financial dealings.[1]
Single Key vs MultiSig
| Wallets / Characteristics | Single Key Wallet | MultiSig Wallet |
|---|---|---|
| Number of Keys | Rely on a single private key for access and control. Transactions from the wallet are authorized with only one signature. | Require multiple private keys to authorize transactions. The number of signatures required depends on the multisig configuration. |
| Security | Lower security. If the single private key is compromised or lost, the funds are vulnerable to theft, with no backup or redundancy. | Enhanced security. An attacker cannot access the funds without the required number of additional signatures. |
| Complexity | Easy to set up. | More complex to set up and manage. Coordinating with multiple parties, handling multiple private keys, and configuring specific security parameters. |
| Recovery & Redundancy | Lacks built-in redundancy. If the private key is lost or compromised, recovery can be challenging, and funds may be permanently lost. | Designed with redundancy. Allows for a backup if, one key is lost or compromised. |
| Transaction Authorization | Authorized solely by the holder of the single private key, allowing for quick and straightforward transactions. | Require the approval of the specified number of authorized signers, adding an extra layer of complexity and potentially increasing transaction authorization time. |
| Security Trade-offs | Simple and convenient, but comes with higher security risks. | Enhanced security, but can be more complex to manage. |
| Use Cases | Suitable for individuals who prioritize simplicity and quick access to their funds. They are often used for everyday spending. | Business accounts, shared family accounts, escrow services, and situations where trust and accountability are essential.[4] |
MultiSig Wallet Attacks
Phishing Attacks
Attackers may impersonate wallet providers or trusted individuals to trick users into revealing their private keys or authentication codes, which can compromise a multisig wallet's security.
Social Engineering
Attackers may attempt to manipulate or deceive one of the authorized signers to gain access to their private key. This can be done through various means, such as impersonation, bribery, or coercion.
Key Theft
If one of the private keys is compromised or stolen, it can be used by an attacker to sign transactions without the knowledge or consent of the other authorized signers. This is a significant vulnerability in multisig wallets.
Inadequate Key Management
Poor key management practices, such as storing private keys in unsecured locations or using weak passwords, can expose multisig wallets to unauthorized access.
Software Vulnerabilities
Vulnerabilities in the wallet software or the underlying blockchain network can be exploited by attackers to gain control of a multisig wallet. It's essential to keep wallet software and firmware up to date.
Physical Attacks
In some cases, physical attacks on the devices or storage media used to store private keys can result in key compromise. Secure hardware storage is essential to mitigate this risk.
Collusion Attacks
In situations where multiple authorized parties are required to sign transactions, collusion attacks can occur if two or more signers conspire to approve fraudulent transactions. Choosing trusted parties for multisig setups is mandatory.
Excessive Trust in One Party
Multisig wallets are designed to distribute trust among multiple parties. However, if one party has significantly more control or access to the keys, it can potentially compromise the security of the wallet.
Smart Contract Vulnerabilities
Multisig wallets implemented using smart contracts can be vulnerable to coding errors or vulnerabilities in the contract's code, leading to unexpected behavior and potential exploits.
Loss of Recovery Information
Multisig wallets often have recovery mechanisms in place, such as backup keys or seed phrases. If these recovery options are lost or compromised, it can be challenging to regain access to the wallet.[11]
MultiSig Wallet Hack Incidents
Bitfinex (2016)
- Bitfinex suffered a high-profile security breach in August 2016. The exchange used a 2-of-3 multisig wallet configuration to secure customer funds.
- Hackers exploited a vulnerability in Bitfinex's multisig wallet software and stole approximately 120,000 Bitcoins, worth tens of millions of dollars at the time.[8]
Parity Wallet Vulnerabilities (2017)
- Parity Technologies, a blockchain software company, experienced multiple security incidents related to its multisig wallet software in 2017.
- In July 2017, a vulnerability in the Parity multisig wallet code led to a hack resulting in the loss of over 150,000 ETH from various projects and individuals.
- In November 2017, another bug in Parity's multisig wallet code caused a freeze of approximately 513,000 ETH held in multiple wallets.
- These incidents raised concerns about the reliability and security of smart contract-based multisig wallets.[9]
Examples
Armory
Armory is the most widely used BTC multisig wallet. It offers various wallet styles and provides built-in protection against certain types of hacks. Users have the option to store private keys offline on USB devices.
Electrum
Electrum is among the oldest multisig wallets for BTC. Its interface is both user-friendly and secure. Electrum is compatible with other wallets like Ledger and Trezor. It utilizes a simple payment verification system and exclusively supports Bitcoin.
BitGo
BitGo is a multisig wallet specifically for Bitcoin, offering a range of helpful integrations. It allows users to integrate their wallets with third-party cryptocurrency exchanges. BitGo's open-source wallet includes free insurance against hacks and is available in both desktop and web versions.
Trezor and Ledger
While these are primarily hardware wallets, they also provide multisig solutions when used in combination with compatible software wallets.
[6][7]
Safe
Safe(formerly, Gnosis Safe) is a product developed by Gnosis. It is a customizable multisig wallet infrastructure that functions as a smart contract wallet on Ethereum. It requires a predefined number of approvals before executing a transaction and supports various tokens, including ETH, ERC-20, and ERC-721. Safe is governed by SafeDAO, a decentralized collective known as Safe Guardians. [12]
See something wrong?
